Most of the time when we’re thinking about security of information systems, we’re usually only concerned with digital security. And in doing so, we leave open the biggest vulnerabilities of all: Humans. Some of the biggest hacks of all time were made possible by social engineering.
The aim of the following few tutorials is to get you thinking about how we as humans are ultimately the weakest links in even the most secure systems. We’re going to take a look at a few human behaviors which make us vulnerable to social engineering. These are things that we all have in common, behaviors and characteristics we all possess, things that you may never have thought of as a weakness. When it comes to exploiting humans, the very things that make us human also make us vulnerable.
Social engineering is nothing new. In fact, as we’ll see in a minute, it is literally thousands of years old. Social engineering is everywhere and it goes far beyond hacking.
- The infomercials on the TV trying to sell you something
- Children guilting their parents into buying them a toy
- An email from the Nigerian Prince promising you riches
- A bank robber with a fake gun hidden under a cloth
All these and more come under the domain of social engineering. Now let us begin our journey by starting at the very beginning.
History of Social Engineering
The Trojan Horse is a classic example of social engineering at it’s best. To understand it’s genius, we need to go back to 1188 BC.

The Trojan war is coming to an end. After a fruitless 10 year long siege on the city of Troy, the Greeks decided to get creative. They constructed a huge wooden horse and filled it with a select force of men and left it as an offering to the city. Then they promptly pretended to sail away. The Trojans retrieved the horse, dragging it into the walled fortress as a symbol of their victory. As the day came to an end, the soldiers emerged from the Trojan horse and got to work. Under the cover of night, the rest of the Greek army had sailed back and were greeted by open doors. The city was conquered.
It became a major and decisive victory for the Greeks and it was all because of a trick. The Greeks had fooled the Trojans into thinking that were making a gesture of goodwill, a token of defeat. In reality however, they were relying on the Trojans letting their guard down and being foolish enough to think that the Greeks had indeed surrendered.
The Trojan war was won by a social engineering attack. And the rest is now history.
This is a common pattern that we’ll see over and over in different social engineering techniques. It all hinges on the attacker’s ability to make the victim believe something while making it seem like the victim is the one in control. And when the victim is at their most vulnerable, the attacker’s true intentions are revealed.
What is Social Engineering?
Social engineering is the psychological manipulation of people into performing actions or divulging confidential information for the attacker. , making the victim do things that they wouldn’t otherwise have done. Social engineering is an attack vector, a means to an end; It is not the goal but a way to get there.
Humans are the soft center within the hard shells of all modern security systems. Cracking the humans is often a lot easier than cracking these systems.
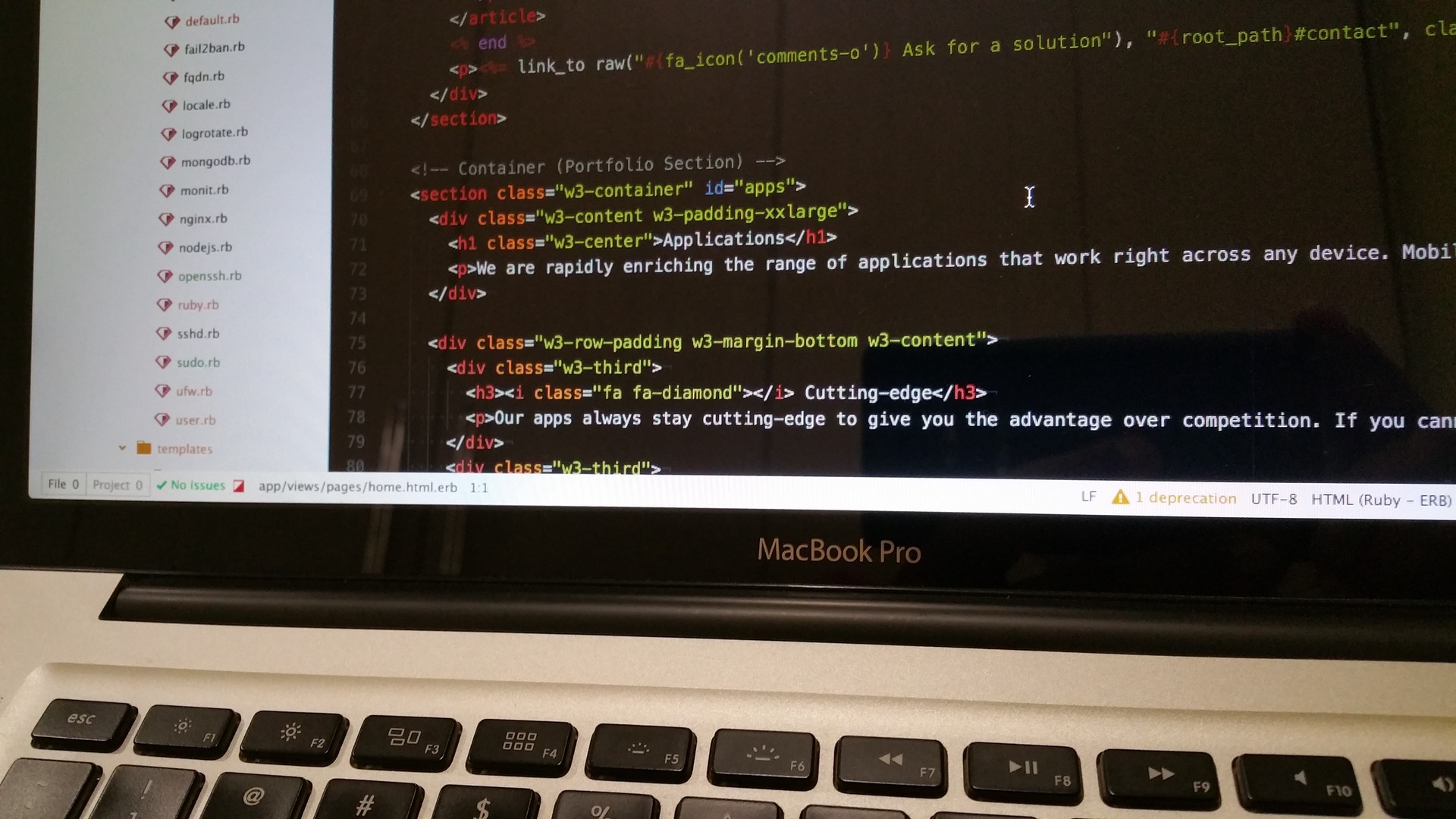
- Firewalls: Hardly any operating systems today come without a built-in firewall. You can find them in servers, in desktops and in routers. There are even dedicated firewall devices for protecting corporate networks. Security firms spend a huge amount of money on developing firewalls and for good reason. Firewalls form the first line of defense, the hard shell that a hacker must break through in order to gain access to a system.
- Authorization Rules: Your pins and passwords (and fingerprints) are what give you access to your devices and all your online accounts. Authorization is the cornerstone of digital security. Unless you can prove your identity you are denied access to the system, thwarting any attacks before they can even begin. This is what keeps your Gmail and Facebook accounts secure.
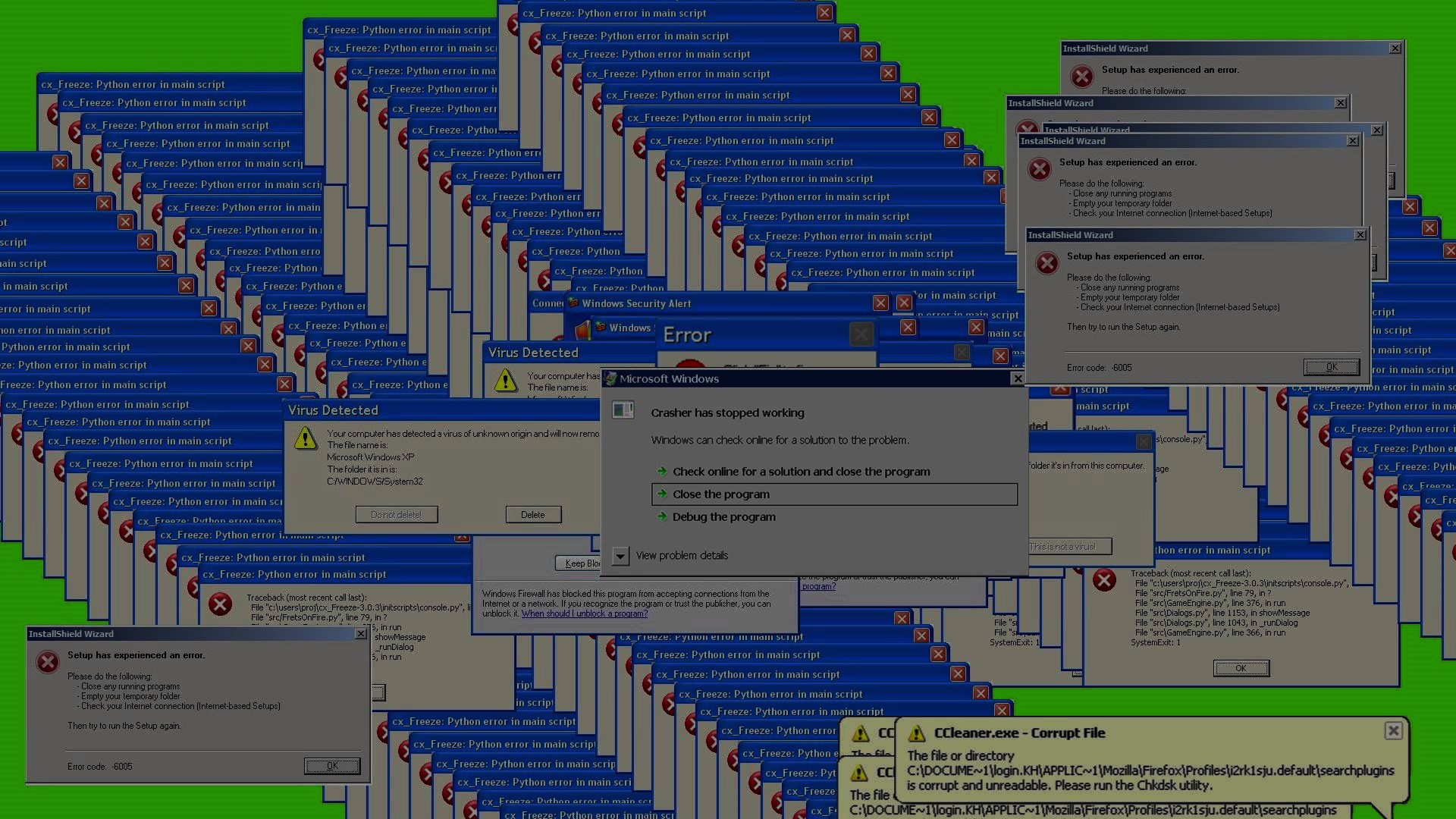
- Anti-virus: Anti-viruses have become a necessity on popular, commonly targeted operating systems such as Microsoft Windows. The job of an anti-virus is to know common malicious software patterns, to watch out for any suspicious files that matches these patterns and to catch them before any damage is done.
These three in particular are a rather common sight in almost all security systems. They are the default security controls in place on the vast majority of systems today. And this is where social engineering comes in. Within these hard shells are the vulnerable humans. The people inside the protection of these security measures who have legitimate access to use the protected system freely, potentially bypassing their otherwise impenetrable shields. .
A company can spend hundreds of thousands of dollars on firewalls, intrusion detection systems and encryption and other security technologies, but if an attacker can call one trusted person within the company, and that person complies, and if the attacker gets in, then all that money spent on technology is essentially wasted.
And this is just what social engineering is: How can the vulnerable humans be exploited to circumvent even the toughest of security measures. Our first step is to better understand the security holes before we can begin exploiting it. Let’s head over to the next one and learn more about the weaknesses of humans.
Want to be a real hacker? Sign Up!