Kali has had a bigger and broader impact on the field of security than anything else. It represents the absolute peak of our understanding of both hacking into systems as well as protecting them from being hacked. Kali is packed with around 300 unique tools that can allow us to penetrate a diverse variety of systems, from smartphones to WiFi networks to web applications to practically everything digital.
It is the home of hackers. Every true security professional uses it. No other operating system even compares when it comes to the sheer power Kali provides us for hacking and penetration testing.
Over the years, I’ve read dozens of books of books on Kali and it’s predecessor BackTrack. I even remember the very first beta of BackTrack back in 2006. We have come a long way since then. The abilities of Kali are exponentially greater than what BackTrack ever had. And Kali is continually evolving. .
The books you’ll find below have been carefully picked and are among the best you can find for learning Kali. Each one serves a unique purpose and each one will bring you one step closer to becoming a true hacker, a master of Kali.
So let’s get started.
1. The Linux Command Line: A Complete Introduction
First up, we’re going to start you off with a plain Linux book (not Kali). If you’re already familiar with working with Linux operating systems such as Ubuntu, feel free to skip this one. This book is meant for beginners who are completely new to the Linux environment. Kali after all, is just a flavor of Linux. Before you learn hacking, you must get comfortable using the command line and that is just what this book focuses on. By the time you’re done with this, you’ll wonder why you never bothered to learn terminal commands before. Get it here.
2. Kali Linux Network Scanning Cookbook
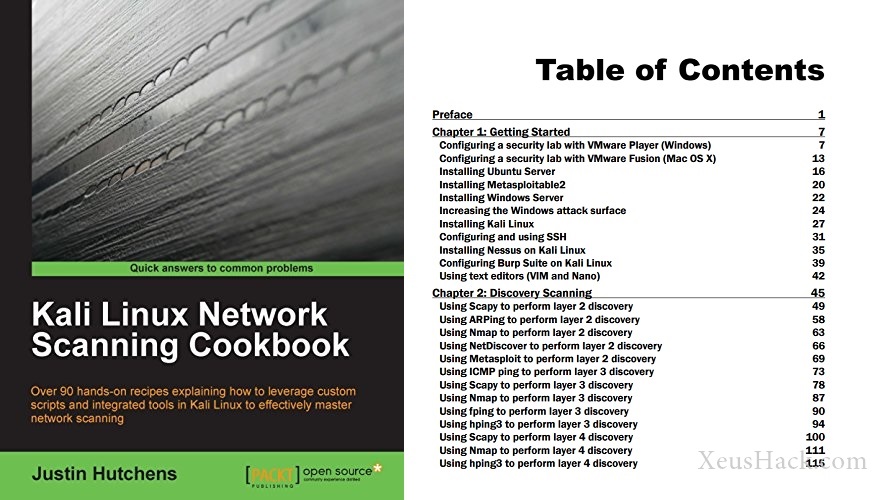
Hacking, or rather penetration testing is defined by three major phases: Information Gathering, Vulnerability Assessment and Exploitation. This book focuses on the first stage: Information gathering and reconnaissance. This one builds upon the commands you learned from the books above. It teaches you a variety of custom network scanning techniques based on real life scenarios that you’re almost definitely going to encounter when you start hacking on your own. It gives you everything you need to learn everything there is to learn about your victim’s system so that you can get to exploiting it quickly. Grab it here.
3. Basic Security Testing with Kali Linux 2
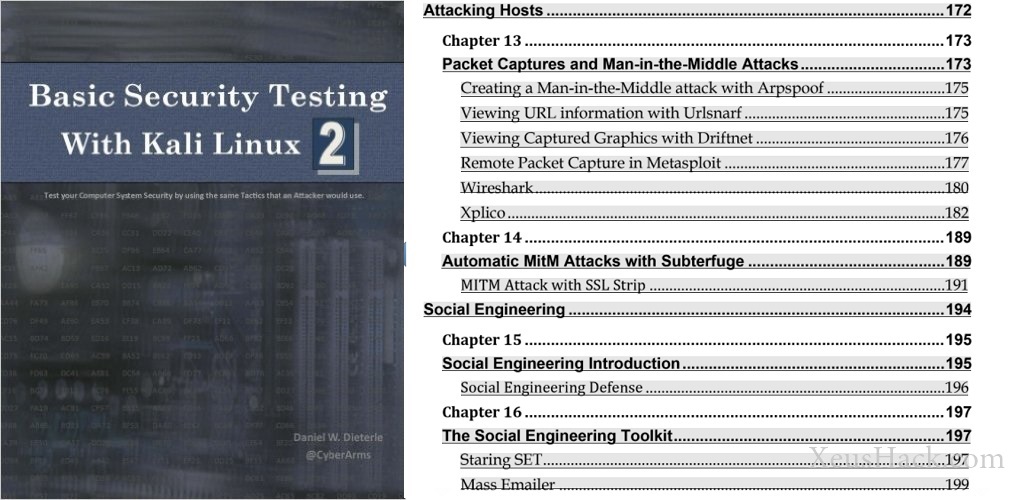
This book gives you the big picture. After the previous two books you should now have an excellent handle on working with Kali Linux. Now’s the time to fly out of the nest and that is what this book gives you. This is where you’ll learn why Kali is so popular. Following are a few topics that the book covers.
- Shodan (the “Hacker’s Google”)
- Metasploit Tutorials
- Exploiting Windows and Linux Systems
- Escalating Privileges in Windows
- Cracking Passwords and Obtaining Clear Text Passwords
- Kali on a Raspberry Pi
- Securing your Network
An easy yet challenging read, after this book you’ll no longer be a beginner. The author focuses on making the reader practice which is just what you need so that you hack all on your own. You can find this book here.
4. Kali Linux Wireless Penetration Testing: Beginner’s Guide
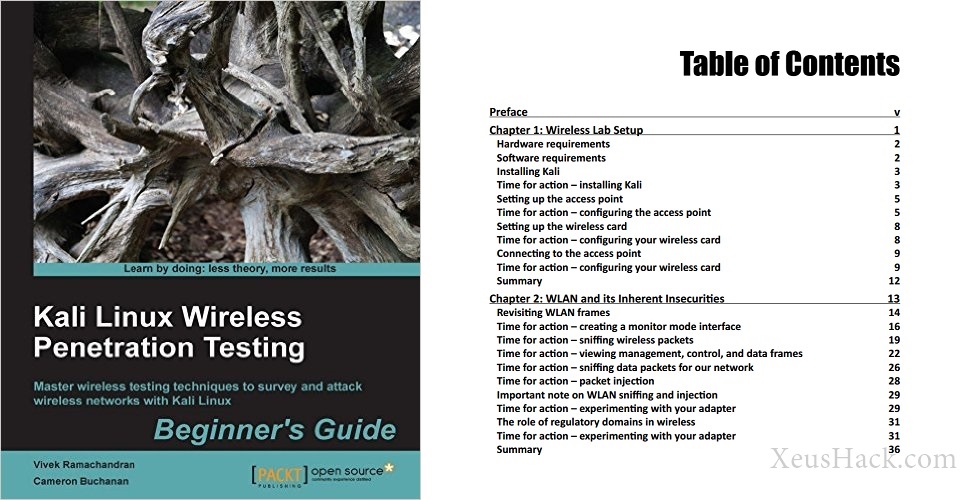
Now we can begin to specialize, this book focuses on a narrower yet extremely important field: Penetrating Wireless Networks. Wi-Fi is everywhere and with the help of this book you’ll be equipped with the tools you need to hack Wi-Fi networks. Here’s what you will learn
- Sniff out wireless packets and hidden networks
- Capture and crack WPA-2 keys
- Discover hidden SSIDs
- Explore the ins and outs of wireless technologies
- Sniff probe requests and track users through SSID history
- Attack radius authentication systems
- Sniff wireless traffic and collect interesting data
- Decrypt encrypted traffic with stolen keys
Essentially everything you need to learn how to hack Wi-Fi networks. Sounds awesome? Get the book from here.
5. The Web Application Hacker’s Handbook: Finding and Exploiting Security Flaws
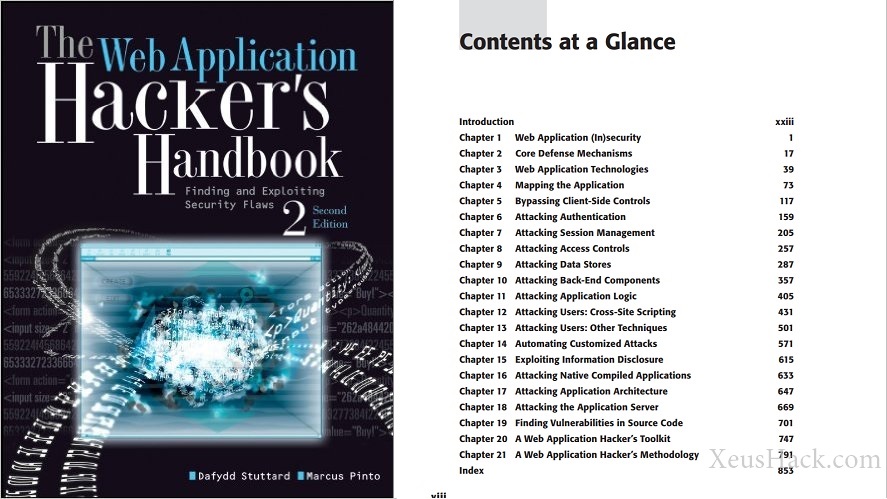
And the last one is also the most powerful one, perhaps one of the best books in the entire field of hacking (not just Kali). This technical book outlines the process of breaking into web based applications (think Google or Facebook). At a hefty ~900 pages, this will certainly require serious effort on your part, but the reward is definitely worth it. This is the single most up-to-date resource on web application penetration testing. It takes you on a journey with the latest technologies used on the internet today and teaches you how to find and exploit security holes in them. You can find the book here.
With these books under your belt, your knowledge of Kali Linux will be on par with the most experienced hackers and penetration testers out there. So, do you think you’re up for it?
P.S: I’ll routinely update this list to account for any new books or editions.
Want to be a real hacker? Sign Up!